How to Install Tor Browser on Windows
One of the great things about the internet used to be the anonymity of it. You have the freedom to share information without compromising your privacy. However, with technology becoming ever better, it is becoming increasingly difficult to stay hidden on the web. If you are looking for privacy over the web, look no further than using Tor.
What Tor is
What is Tor and how does it work? To fully understand Tor, it needs be broken down into separate parts. That first part is called onion routing. Onion routing is a system designed to block any kind of efforts to track communications. It allows two ends to communicate to each other without letting either party know who exactly they are communicating with. It also ensures encryption.
The second part is the Tor network. The tor network is a large connection of servers that are operated by volunteers. These servers run onion routers that funnel internet traffic through virtual pathways. In simple terms, they scramble the traffic in a way that makes it almost impossible to track who is talking to whom.
The last part is a Tor browser. Most browsers are set up to store information on the user. If you allow your browser to store your password for any site, then it is tracking information on you. The normal browser stores cookie files and browsing history. Both of these are information stored on you so that it can either deliver a better service to you or deliver advertisements based on your general interests. Neither of these support efforts towards privacy.
Installing a Tor Browser on Windows
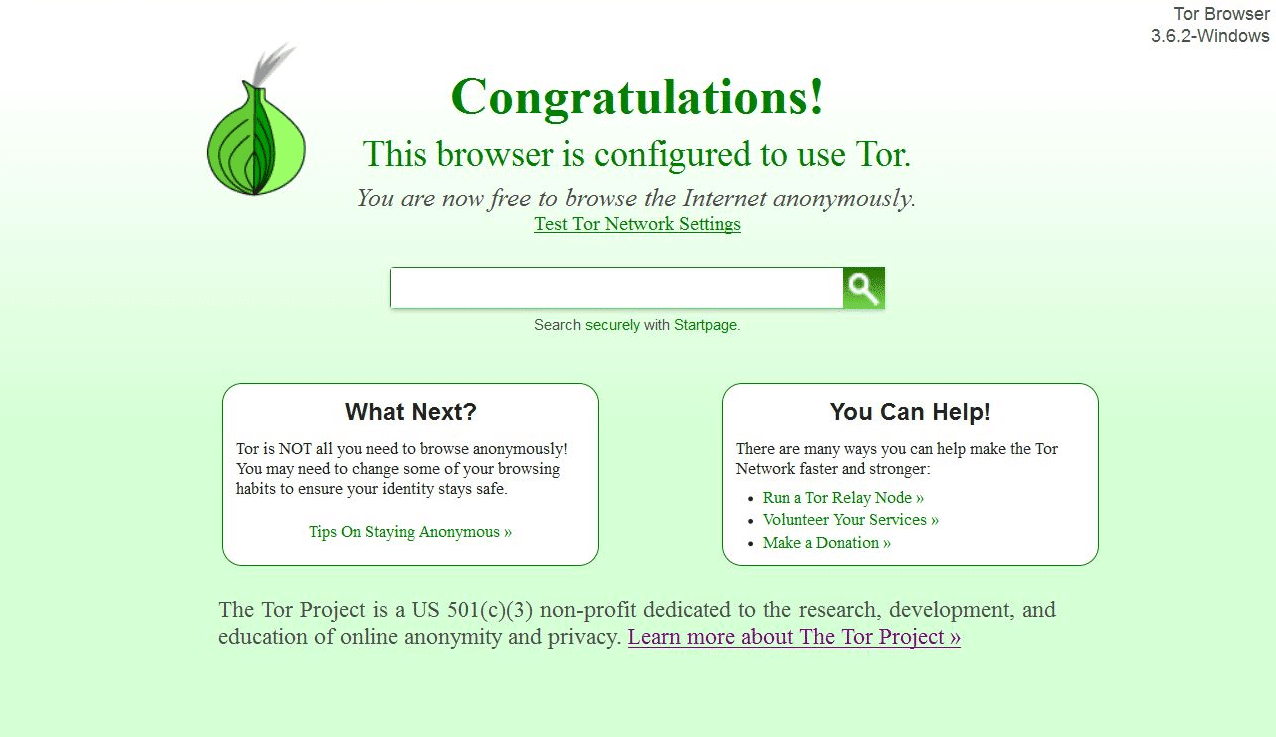
The first step to installing the Tor browser is to go to the website at www.torproject.org/download. Download the version for your operating system. Follow the installation directions in the same way for normal applications. Once the installation is complete, run the browser. From here, you’ll be able browse the internet anonymously with limitations.
There are limitations and considerations to using a Tor browser. First, the tor network only provides privacy and encryption while inside the network. This means that any communication passed once outside the network is vulnerable. Next, the tor browser does not protect all of your computer’s activity. If your computer is not going through Tor then it is not providing anonymity. Also, it does not protect against document downloaded through Tor while online. If you download a document while using Tor, do not open the document. If you must, start a virtual machine and open it within the machine while it isn’t connected to the internet. The last thing is not allowing plugins to run on the Tor browser. Plugin extend the functionality of a browser. However, they are extension that run on your computer that have the ability of opening holes in your security.
The Deep Web
While anonymity can provide a place to freely share ideas, it can also be a source of illegal activity. With that being said, the Tor browser allows you to surf websites that operate illegal and sometime immoral activities. Websites like “The Hidden Wiki” do not censor some material that others may find offensive. To sum it up, Tor browsing offers anonymity but at its price.







1 Comment
This was really helpful. I have used Tor before but never really understood how it worked. Thanks for the great article, it was very educational.